End to end configuration of sensitivity labels to protect content in Microsoft Teams, Office 365 groups, and SharePoint sites.
April 14, 2020 Leave a comment
As of now this feature is in Public Preview!
You can create sensitivity labels in the compliance center and these labels can be applied for the following containers: Microsoft Teams sites, Office 365 groups, and SharePoint sites. As of now we have the following label settings to help protect the content in those containers:
- Privacy (public or private) of Office 365 group-connected teams sites
- External users access
- Access from unmanaged devices
When you apply this label to a supported container, the label automatically applies the configured options to the connected site or group.
Important thing to note – The Content in those containers do not inherit the labels for settings such as the label name, visual markings, or encryption. So that users can label their documents in SharePoint sites or team sites only manually with E3 License.
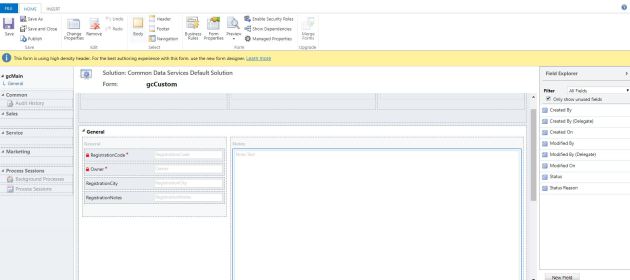
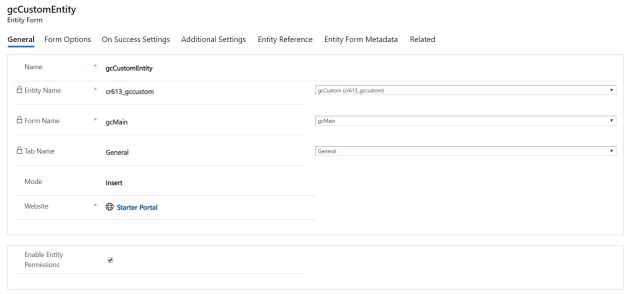
To create Sensitivity label in the Compliance Center –

Here we created two Sensitivity labels one for private and the other for public sites with guest sharing on, on creation of these go with the default options on all except “Site and Group Settings”
Create New Sensitivity Label –

Site and group settings option for company – restriction label with private

Site and group settings option for company – public label with public and guest sharing

We have to publish these labels through label policies –
Always a good practice to publish label to one or two users and test before publishing for the large groups. Also deleting or modifying the label while it’s associated with sensitivity policies can result in team creation failures across the tenant. Therefore, before you delete or modify a label, you must first disassociate the label from its associated policies.

Now go to Azure (portal.azure.com) and try creating an Office 365 group no surprise we don’t see the option to pick a sensitivity label.

So we need to enable sensitivity labels through PowerShell (Link), as it required enabling the feature. If no group settings have been created for this Azure AD organization you get the below error, so you must first create the settings.
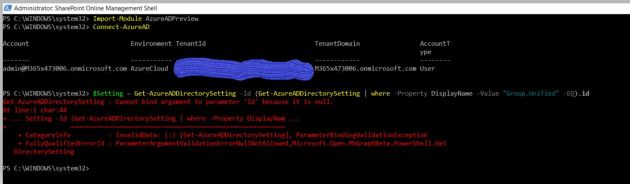
Follow the steps in Azure Active Directory cmdlets for configuring group settings to create group settings for this Azure AD organization.
Important that you uninstall any previous version of AzureADPreview and install the latest version of Azure AD Preview to have this work.
These steps create settings at directory level, which can apply to all Office 365 groups in the directory. Again to configure Office 365 group settings for your directory, you use the template named “Group.Unified”.
So as an example we can add usage guideline URL, for that you need to get the SettingsTemplate object that defines the usage guideline URL value; that is, the Group.Unified template.
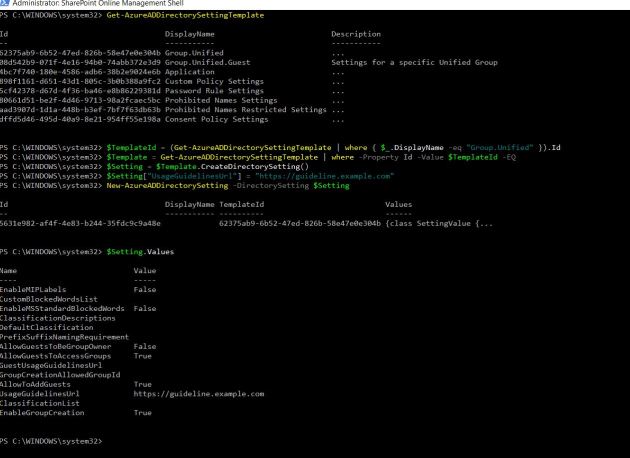
As our objective is to just create group settings for this Azure AD Organization and not to use the UsageGuideline Url, so we are going to reset it to empty. To update the empty value for UsageGuideLinesUrl in the setting template, read the current settings from Azure AD, otherwise we could end up overwriting existing settings other than the UsageGuideLinesUrl.
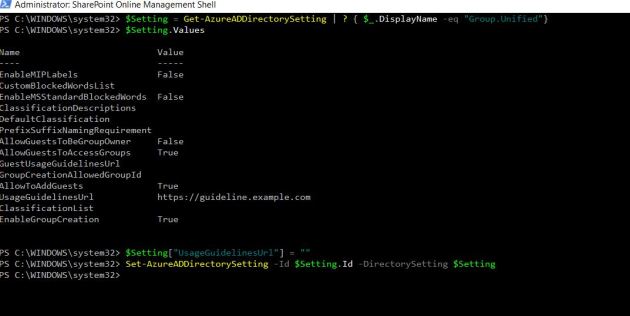
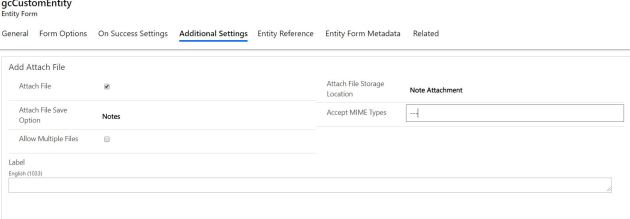
Now the group settings have been created for this Azure AD organization, we can enable the feature through “EnableMIPLabels”. In the following picture we can see that we have Enabled MIP Labels to true.

After enabling mip labels, if we go to Azure and try to create new Office 365 Group; now we will see a new field “Sensitivity label” under Membership type. This is almost instantaneous but to have this to show up in SharePoint it might take around an hour or so as SPO has a caching refresh logic. Also it could take up to 24 hours for your published labels to show up in the Sensitivity label dropdown .

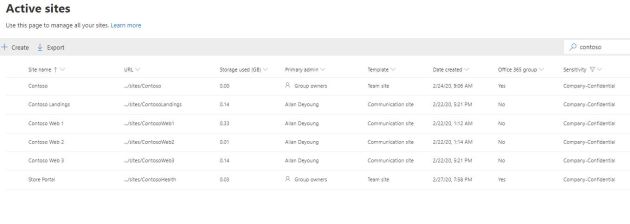
If you want to Apply Sensitivity Labels through SPO Admin center – Select the site and see in the site and go to Policies, there we can see the section for Sensitivity and click Edit under it.
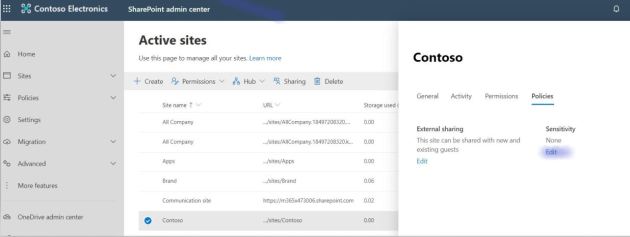
Here you can pick the Label that you want apply to the site (These are the Sensitivity Labels created & published in the compliance center).

After applying the label to the site “contoso” – It changes the public group to private group and the label name “Company Confidentail” would show up.
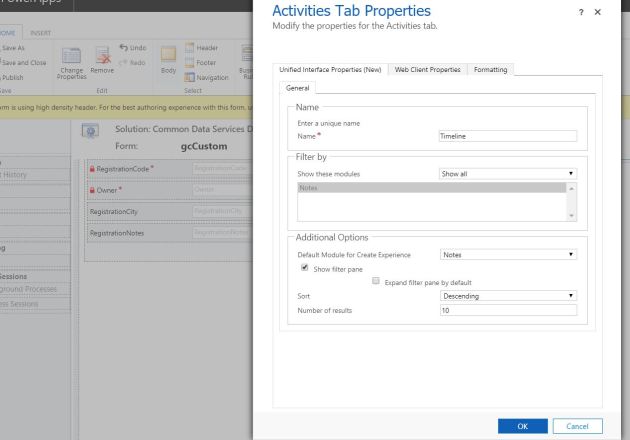
To change the label of the site as a Site owner go the settings – site information

Now we have the label feature enabled and few labels published, so the creating dialog for provisioning Sites/Groups/Teams have the sensitivity option shows up. In Teams if we pick the label company confidential it will only enable the relevant options that comply with the label.
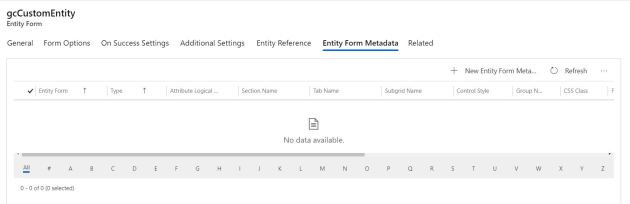
Finally now if we want to go back and apply these labels for several other existing sites, we can do through the PowerShell
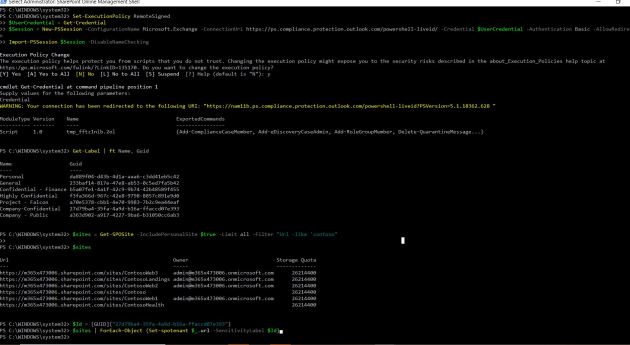
PowerShell Screen shot
If you have a requirement to set “Sensitivity” label for
many site-collections using PowerShell is the most optimized way.
Download the latest SPO admin PowerShell
//For connecting to SPO
connect-sposervice
//Office 365 Security & Compliance Center PowerShell allows you to manage your Office 365 Security & Compliance
Set-ExecutionPolicy RemoteSigned
$UserCredential = Get-Credential
$Session = New-PSSession -ConfigurationName Microsoft.Exchange -ConnectionUri https://ps.compliance.protection.outlook.com/powershell-liveid/ -Credential $UserCredential -Authentication Basic -AllowRedirection
Import-PSSession $Session -DisableNameChecking
//Get the list of Sites that you want to apply Labels
$sites = Get-SPOSite -IncludePersonalSite $true -Limit all -Filter “Url -like ‘contoso”
//That’s the guid of my company confidential label
Get-Label | ft Name, Guid
$Id = [GUID](“27d79ba4-35fa-4a9d-b16a-ffaccd07e393”)
//Apply this sensitivity labels for sites
$sites | ForEach-Object {Set-spotenant $_.url -SensitivityLabel $Id}
We can extend this enabling sensitivity files for office files through the (link)
In the near future we may have few more options available for these labels, so I think it would be worth investing and adopting this in your tenant.
Note: I would really thankful for Sanjoyan Mustafi for his timely response on questions and his snippet on Powershell to apply Sensitivity labels for many sites.